This guest post is brought to you by Armin Kerl, if you fancy trying you hand at blogging check out our guest posting opportunities.
Principle:
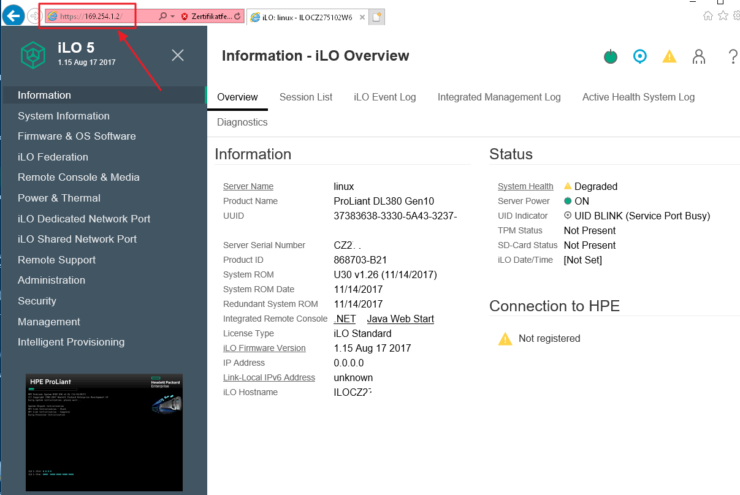
The Gen10 servers now have a 1GB reserved space in the NVRAM for firmware and driver files with iLO 5, it’s called The iLO Repository. We are now able to upload firmware and drivers direct to the iLO NVRAM. This can be *.bin, *.fwpkg for firmware, *.zip for ESX, *.exe for Windows, or *.rpm for Linux.
The Integrated Software Update Manager (iSUT) service in the OS can monitor the iLO repository content. If there is something new, it pulls the update and then installs firmware and drivers inside the OS. A reboot is usually necessary afterwards. No more booting from the SPP ISO Image for firmware updates and you can specify several server stages or even reboot a number of times.
You can get more information at the HPE SUT Site here and in the User Guides
The iLO can be fuelled with updates in several ways, I will explain the most common.
- Upload individually in iLO under the Firmware Tab.
- Launch the Software Update Manager (SUM) from the Service Pack for ProLiant (SPP), and deploy.
- Distribute the SPP with iLO Amplifier.
I will now explain 2 and 3 by using an ESXi server as an example.
Prepare
First, the iSUT must be installed on the target server and set to AutoDeploy. The iSUT should already be installed with HPE ESX Image.
Check It:
[root@SRVESX1:~] sut -status System Update Manager...................: OS Administrator Task Status.............................: Bios:N/A; LocalStorage:N/A; Deploy:Idle Staging Directory.......................: /tmp/sut/stagingdirectory Baseline URI............................: None Baseline Version........................: Waiting for staging Mode of Operation.......................: OnDemand Polling Interval In Minutes.............: 5 Force Deploy............................: No Optional Components.....................: None EnableiLOQueuedUpdates..................: true User Action Needed......................: To perform the firmware updates import the server to OneView or use iLO Amplifier Pack. If imported into OneView create a server profile with a firmware baseline and apply the profile to the server. iLO Security Mode.......................: Production iLO CAC Smartcard Authentication........: Off iLO CAC Strict Mode.....................: Off Now set iSUT to Deploy Updates:
[root@SRVESX1:~] sut -set mode=AutoDeployReboot Set Mode: AutoDeployReboot Service will be registered and started Service already registered SUT Service started successfully Registration successful
You can set the iSUT mode to AutoDeployReboot mode.
However, iSUT reboots the VMware ESXi host only if the host is in maintenance mode.
If it is not Installed, Download HPE Utilities Offline Bundle for ESXi 6.7
Use Service Pack for ProLiant
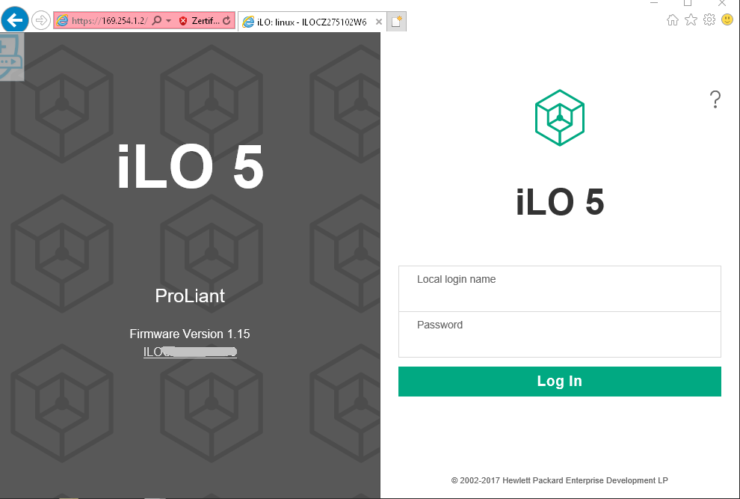
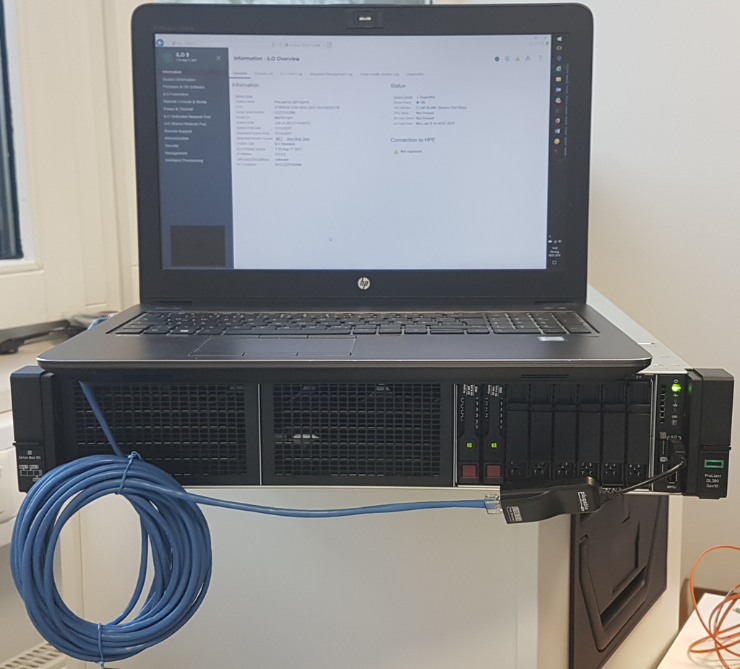
Mount the SPP ISO on the deployment PC/server and start SUM with launch_sum.bat.

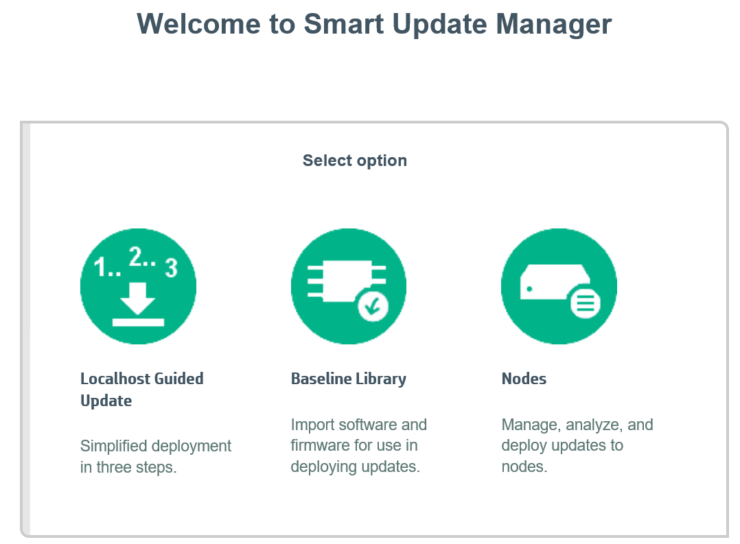
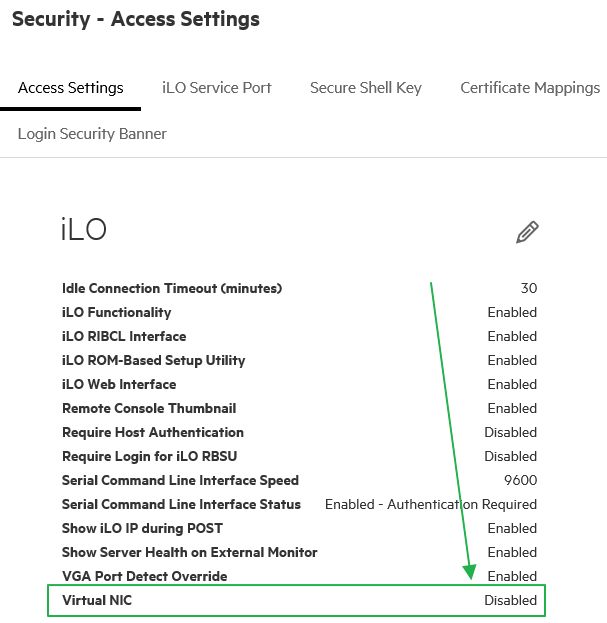
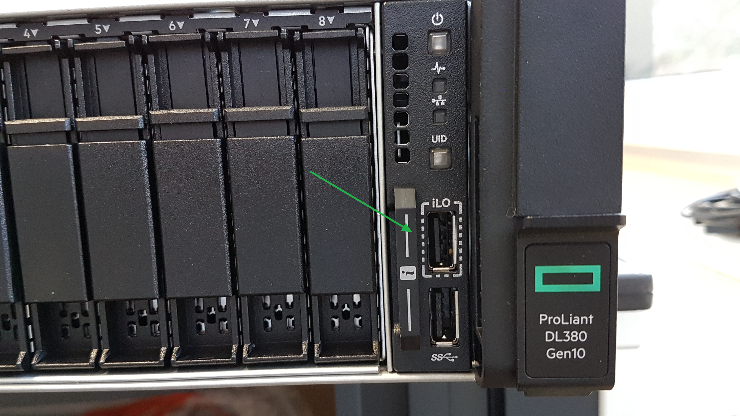
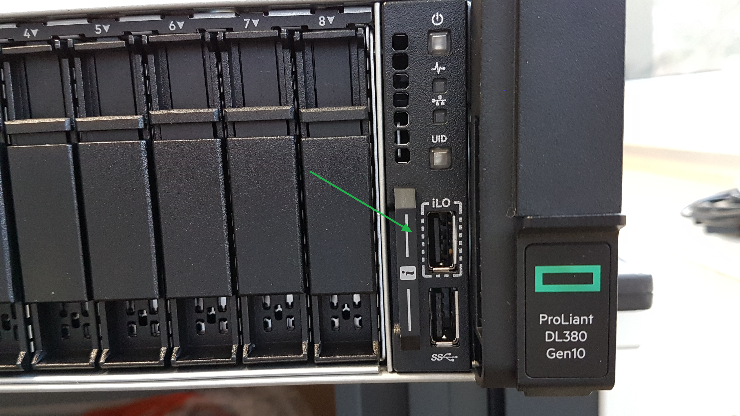
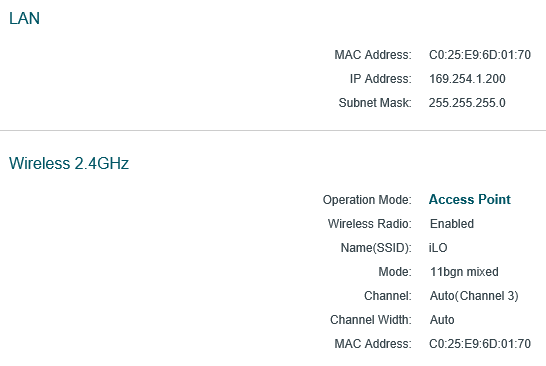
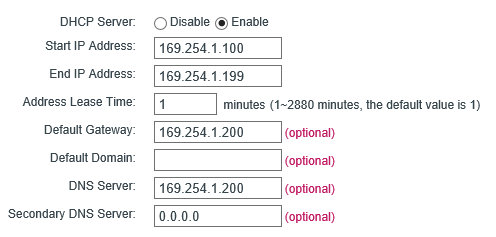
Select Nodes and add your Target Server using the iLO IP, not the OS IP.
Node Type: iLO
Baseline: Your Service Pack ProLiant

Now, first Start an Inventory and then choose Deploy.


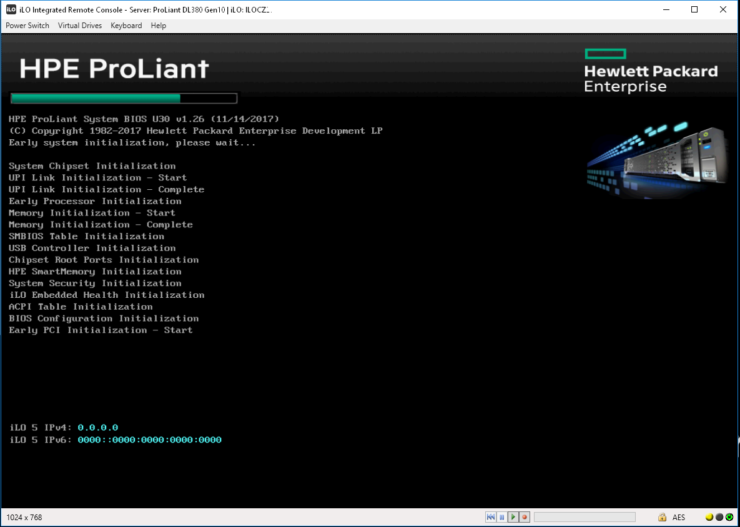
Chose to Deploy and the SUM will copy the Firmware and Drivers to the iLO NVRAM.
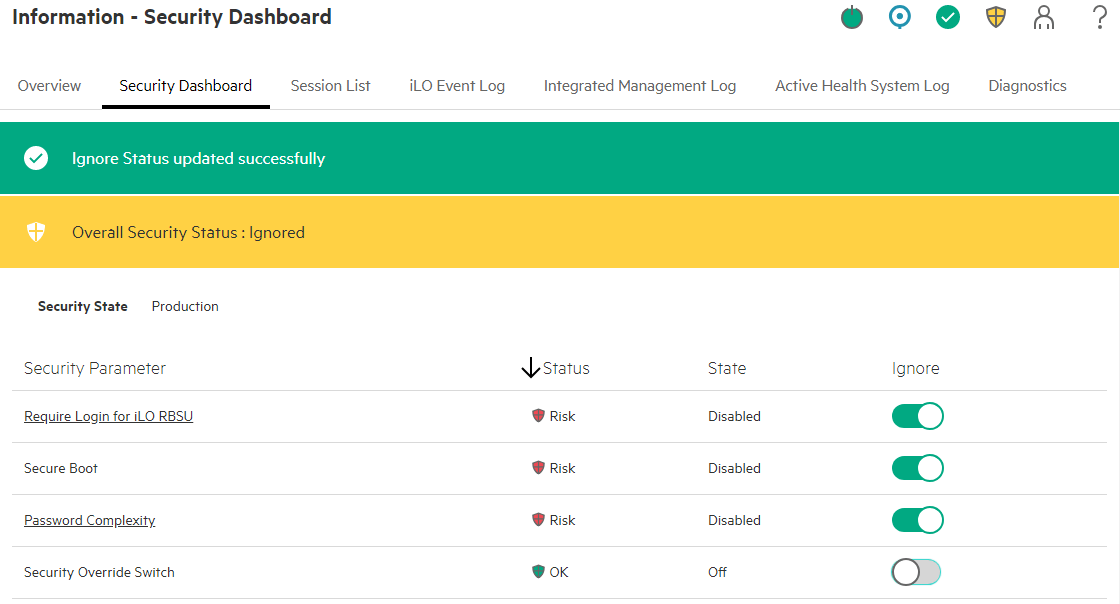
You can watch this in the iLO GUI:


The iSUT Service in the OS will now pick-up software from iLO and install.
When all is done, reboot the host, and you are done.

With iLO Amplifier
https://iloamplifierpack.itcs.hpe.com/
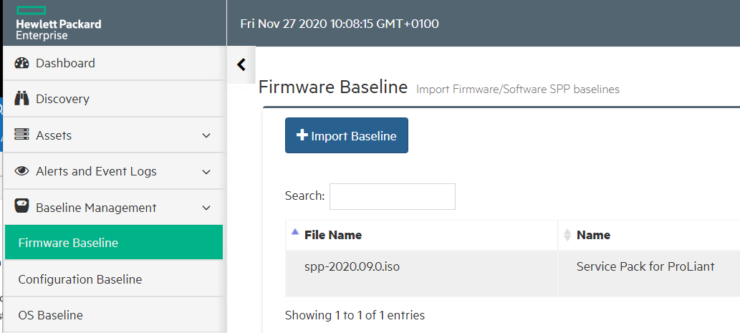
First, we must upload the SPP to the iLO Amplifier Repository.
This is done, by Firmware Baseline > Import Baseline:


Now we can Rollout the SPP to the Servers.
Select “Server Updates”:

If you see “SUT mode not supported, SUT not running. Host OS type not supported, AMS not Running.” the server is usually powered Off.
If you see “SUT mode not supported. SUT not running or “ iSUT is not enabled, you need to refresh the Server state using Assets > Servers > Select Server > Action > Refresh.

From this point, it is the same as with SUM.
The Files are being copied to the iLO NVRAM, iSUT will see and then install them.